- Cybersecurity is a proper legitimate procedure for protecting every category of data from theft and damage. This specific procedure targets at protecting sensitive data, personally identifiable information (PII), personal information, intellectual property, data, and governmental and industry information systems respectively.
- In the present scenario, there is a need for Cyber-Security implementations as cybercrime is increasing hugely. In fact, the demand for cyber-security solutions has risen gradually in the manufacturing, government, and healthcare sectors respectively. Over the years, bolstered the market's growth. It is being speculated that in the coming years it will even grow more. And you must acquire professional training if your interest lies in this field.
Here, at Croma Campus, you will get the opportunity to acquire in-depth training in this course by our experienced faculty members.
Our faculty members will help you to enhance your communication by indulging you in numerous discussions, and interactions concerning the subject.
You will get access to our LMS portal, where you will find class teachings, assignments, etc.
You will be given enough study material also.
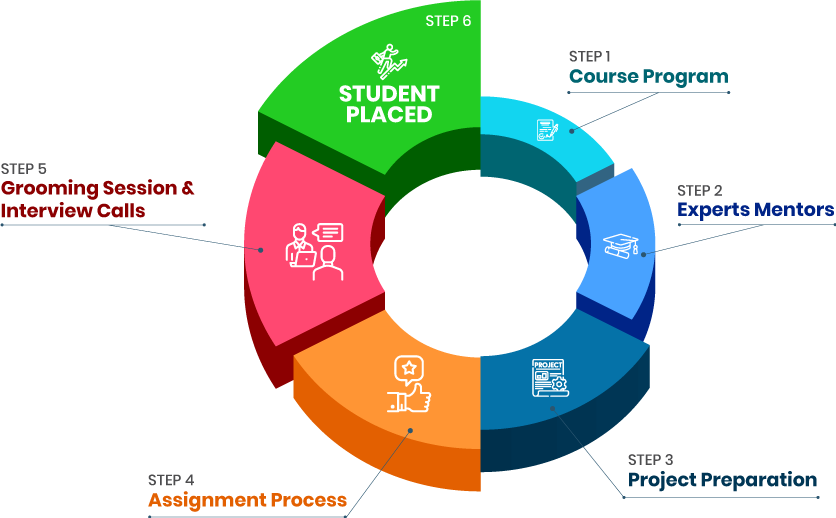
Post completing the course, our trainers will put you through the placement process.
- The Cyber Security Course in Delhi is one of the most interesting courses belonging to the IT domain. It has a bright scope ahead also. Moreover, if you want to turn into a successful Ethical Hacker, then you should surely get started with its professional course.
Well, right at the beginning of the course, our trainers will first let you know the fundamentals of this course.
Furthermore, you will receive sessions regarding its enterprise architecture and elements.
Our team will also let you know the information system, governance, and risk assessment.
Moreover, you will be given a quite qualitative session regarding the incident management section as well.
- Cyber-security is quite an evolving field and has been expanding at a rapid rate. There's a misperception of people that this specific field is not a well-paid job, which is eventually not true.
By obtaining this specific certification in hand, you will earn around 3.5 Lakh Per Annum, which is quite good for starters.
By gaining more experience in this field, your salary structure will eventually get better.
Your chances of getting into a well-established company will also increase.
You will always receive a higher salary structure than normal employees.
- At the moment, it is one of the flourishing fields that has a bright scope ahead. One of the highlighting benefits of this course is that it offers a various list of job roles.
Obtaining this certification will help you to acquire the exact exposure to this field.
It will help you to grab a much higher salary package than other employees.
You will be able to work professionally as a Penetration Tester, Ethical Hacker, Cyber-Security Engineer, Security Analyst, etc.
Your chances of getting into a well-established company will also increase.
This accreditation will help you to sustain yourself in this direction in the long run.
- Cybersecurity has a vibrant future ahead, and you must learn Cyber Security Course to know the latest trends and features concerning this technology.
By learning this course, your impression will reflect differently in front of the interviewer, and you might end up getting into a good workspace.
You will get an opportunity to work with government secret agencies
You will come across various job opportunities.
In fact, you will get the chance to choose from a wide range of industries.
- A Security Analyst has to perform a series of tasks to secure the data of the company. Moreover, if you also wish to become a successful Security Analyst or an Ethical Hacker in near future, then you should know some of the main job roles of this designation.
Working as a Security Analyst will indulge you in securing the overall information security of your company.
You will also have to assure internet security for individuals and organizations as well.
You will have to keep reviewing the data regularly.
Paying attention to minute details of the data will also be counted as your main job role.
- Currently, you will find loads of IT companies hiring skilled Security Analysts or Ethical Hackers to protect your systems and data. Choosing this course will eventually allow you to make a place for yourself in this domain.
Breter Managings, Pearson, Adobe, Zoylee, etc. are top-most companies hiring skilled Security Analysts.
Here, we will assist you to get into established organizations.
In fact, our team will consecutively help you in resume building, appearing in front of the interviewers, and more.
Our trainers will also enhance your communicative skills.
- Well, Croma Campus is a bona-fide institution dealing in imparting a standard sort of training for years. Here, our team will help you to understand the minute details of this course in a better way.
Our trainers will help you to pass the interview round.
Our trainers will prepare you to crack the interview procedure by conducting mocks tests, and assignments as well.
You will also get a proper brief of other courses, and certifications respectively.
- You May Also Read:
Why Should You Learn Cybersecurity?
By registering here, I agree to Croma Campus Terms & Conditions and Privacy Policy
 Course Duration
Course Duration
30 hrs Hrs.
Flexible Batches For You
26-Apr-2025*
- Weekend
- SAT - SUN
- Mor | Aft | Eve - Slot
28-Apr-2025*
- Weekday
- MON - FRI
- Mor | Aft | Eve - Slot
30-Apr-2025*
- Weekday
- MON - FRI
- Mor | Aft | Eve - Slot
26-Apr-2025*
- Weekend
- SAT - SUN
- Mor | Aft | Eve - Slot
28-Apr-2025*
- Weekday
- MON - FRI
- Mor | Aft | Eve - Slot
30-Apr-2025*
- Weekday
- MON - FRI
- Mor | Aft | Eve - Slot
Course Price :
Timings Doesn't Suit You ?
We can set up a batch at your convenient time.
Program Core Credentials
Trainer Profiles
Industry Experts
Trained Students
10000+
Success Ratio
100%
Corporate Training
For India & Abroad
Job Assistance
100%
Batch Request
FOR QUERIES, FEEDBACK OR ASSISTANCE
Contact Croma Campus Learner Support
Best of support with us
CURRICULUM & PROJECTS
Cybersecurity Certification Training
- Introduction
- Identity and Access Management, Cryptography And PKI
- Identification and Authentication, Identity and Access Services
- Technologies, Tools, Architecture, and Design
- Risk Management
- Network Fundamentals, Securing the Network
- Introduction to Cyber Security
- Need of cybersecurity
- Why is Security Important
- Security Policy, Threat Actor Types
- Identifying Security Fundamentals
- Implement secure network architecture concepts
- Malware and Indicators of Compromise
- Attacks, Threat Actors
- Vulnerability Scanning and Penetration Testing
- Vulnerabilities and Impact
- Security Tools and Technologies
- Troubleshoot Common Security Issues
- Implementing Secure Protocols
- Social Engineering, Technical, Wireless and Cryptographic Attacks
- Crypto-malware, Ransomware, Worm, Trojan
- Uses of Cryptography
- Cryptographic Terminology and Ciphers
- Cryptographic Products
- Overview to photographic, Methods Symmetric Cryptosystems
- Public Key Infrastructure, Cryptographic Attacks
- Symmetric Block Modes
- Install and configure identity and access services
- Identity and Access Management Controls
- Cryptography Concepts, Cryptography Algorithms
- Wireless Security
- Public Key Infrastructure
- Understand all security essentials from cryptography to risk management
- Symmetric, Asymmetric Encryption
- Creating File Hashes
- Installing a Certificate Authority
- Access Control Systems
- Identification, Authentication
- LAN Manager / NTL
- Kerberos
- PAP, CHAP, and MS-CHAP
- Password Attacks
- Token-based Authentication
- Biometric Authentication
- Common Access Card, Authorization
- Directory Services
- RADIUS and TACACS+
- Federation and Trusts
- Federated Identity Protocols
- Installation and configuration of network security devices
- Analyze and interpret output from security technologies
- Troubleshoot common security issues.
- Firewall, VPN concentrator, NIPS/NIDS
- Protocol analyser, Network scanners
- Wireless scanners/cracker, Password cracker
- Secure Systems Design Secure Mobile Device Services
- Secure Virtualization and Cloud Services
- Secure Network Design
- Secure Network Design
- IDS and SIEM
- Site Layout and Access
- Secure Wireless Access
- Secure Protocols and Services
- What is Risk, Analyzing Risk, Managing Risk
- Risk Management and Business Impact Analysis Concepts
- Business Impact Analysis
- Identification of Critical Systems
- Risk Assessment, Risk Mitigation
- Policies, Plans and Procedures
- Incident Response, Disaster Recovery and Continuity of Operation
- Secure Application Development
- Data security and privacy practices.
- Standard operating procedure
- Agreement types
- General security policies
- Data sensitivity labeling and handling
- Using TCP/IP Tools
- Configuring a Firewall
- Examining Website Certificates
- Securing a WAP
- Viewing Event Logs
- Scanning the Network
- Securing Hosts and Data
- Enabling BitLocker
- Securing Network Services
- Disaster planning and recover
- Access Control
- Managing NTFS Permissions
- Managing Active Directory Objects
- Start applying for Jobs
+ More Lessons
Mock Interviews
Phone (For Voice Call):
+91-971 152 6942WhatsApp (For Call & Chat):
+919711526942SELF ASSESSMENT
Learn, Grow & Test your skill with Online Assessment Exam to
achieve your Certification Goals

FAQ's
Yes, it's one of the most demanding courses as it protects your data.
They earn quite well. Normally, their salary is around 6 Lakhs as per different job roles.
- - Build an Impressive Resume
- - Get Tips from Trainer to Clear Interviews
- - Attend Mock-Up Interviews with Experts
- - Get Interviews & Get Hired
If yes, Register today and get impeccable Learning Solutions!

Training Features
Instructor-led Sessions
The most traditional way to learn with increased visibility,monitoring and control over learners with ease to learn at any time from internet-connected devices.
Real-life Case Studies
Case studies based on top industry frameworks help you to relate your learning with real-time based industry solutions.
Assignment
Adding the scope of improvement and fostering the analytical abilities and skills through the perfect piece of academic work.
Lifetime Access
Get Unlimited access of the course throughout the life providing the freedom to learn at your own pace.
24 x 7 Expert Support
With no limits to learn and in-depth vision from all-time available support to resolve all your queries related to the course.
Certification
Each certification associated with the program is affiliated with the top universities providing edge to gain epitome in the course.
Showcase your Course Completion Certificate to Recruiters
-
Training Certificate is Govern By 12 Global Associations.
-
Training Certificate is Powered by “Wipro DICE ID”
-
Training Certificate is Powered by "Verifiable Skill Credentials"































 Master in Cloud Computing Training
Master in Cloud Computing Training